Sharing is caring!
Website vulnerability scanning
Identify your Website weaknesses and vulnerabilities, before the hackers do.
We perform vulnerability assessment to identify possible security weaknesses in your digital infrastructure, to avoid costly data breaches. We can also investigate whether your email address has been spoofed or pawned.
Here, we have some examples of threats that vulnerability assessment can eliminate are:
- SQL injection, XSS or other attacks with code injection.
- Privilege escalation is caused by faulty user authentication.
- Unprotected defaults, such as a discoverable admin password, are applications that arrive with vulnerable configurations.


What is Vulnerability Assessment
A vulnerability evaluation is The systematic analysis of security vulnerabilities. It examines if the system is vulnerable to any security vulnerabilities, defines severity levels to such vulnerabilities, and, if and whenever appropriate, recommends abatement or mitigation.
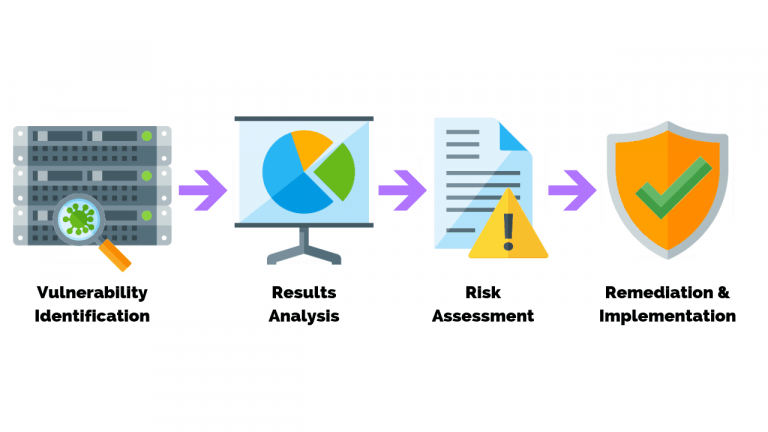
Vulnerability assessment: Security scanning process
1. Vulnerability Identification (Scanning)
The goal of this phase is to formulate a detailed list of the vulnerabilities of a program. Cybersecurity experts test and assess the security performance of databases, repositories or other structures by testing them with automated software. To determine safety vulnerabilities, analysts often depend on vulnerability databases https://canceltimesharegeek.com/, manufacturer vulnerability notifications, wealth management systems, and threat detection feeds.
2. Analysis
The aim of this phase is to determine the cause and root cause of the established vulnerabilities in level one.
It includes the description and the root cause of the insecurity of sensing devices essential for the vulnerabilities. For instance, a previous version of a free software repository might be the root cause of a vulnerability. This offers a straightforward direction for updating the library for remediation.
3. Risk Assessment
Prioritization of exploits is the purpose of this stage. It implies security analysts granting each vulnerability a rank or intensity ranking, predicated on such considerations as:
- The systems that are influenced.
- What data is at risk.
- Which are at risk for business activities.
- Attack or surrender convenience.
- The Severity of an assault.
- Additional damage from the security vulnerabilities as a consequence.
4. Remediation
The purpose of this move is to close security loopholes. It’s usually a collaborative effort between security personnel, management and operations leaders, who decide the most appropriate route for abatement or containment of each vulnerability.
Specific steps for remediation can include:
- Identification of new methodologies, initiatives or tools for security.
- Reviewing of alterations to functional or configuration.
- Advancement of a security vulnerabilities bug fix and deployment.

